Purpose
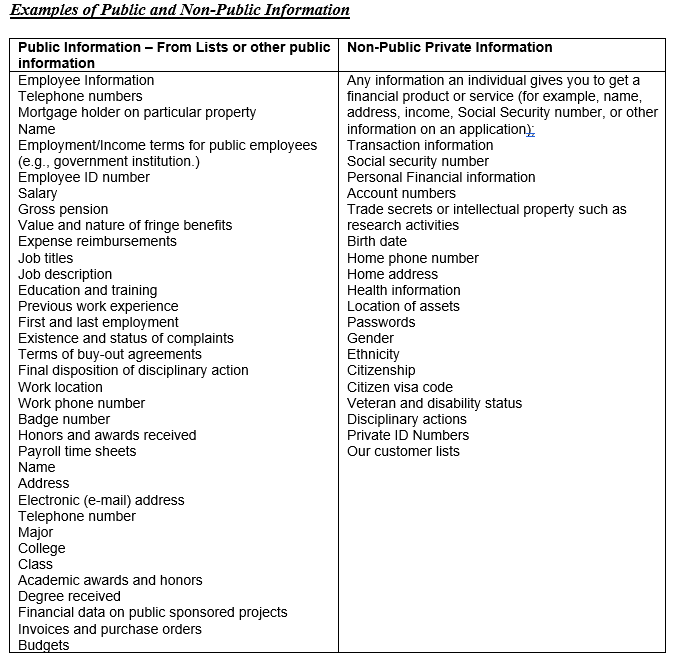
Before inventorying computers, vendors, or networks, small consumer financial companies must first understand what makes them a target. That answer is NPI.
This step is intentionally simple and non-technical.
Step-by-Step
List the types of customer information you touch:
Loan applications
Credit reports
Pay stubs and tax returns
Bank statements
IDs and SSNs
Identify how you encounter NPI:
On your desk (printed documents)
In email (attachments, PDFs, screenshots)
In your LOS or CRM
During phone calls or in-person meetings
Ask one perspective-shifting question: If this data were stolen, what would it be worth on the black market?
Why This Matters
Consumer Financial Services companies are data-rich and security-light. Simply recognizing the volume and sensitivity of NPI reframes cybersecurity from “IT problem” to “business risk.”